Pruebas de VPN detrás de una
router con IP dinámica y realizando PAT
Fecha: Octubre 2012
Clase: ASA Fundamentals (clase privada)
Las pruebas se realizaron entre un ASA 5505 y contra un terminador Cisco 1841, pero las configuraciones
son similares en cuanto al funcionamiento de IPSec, varían detalles de los comandos entre IOS y ASA.
Escenario

En este escenario, se simula una conección a internet con IP dinámisca, tipo ADSL o cablemodem, entre
un Cisco 1841 (abajo en la foto) a travéz de un SW 2960 y se le cambian las IP públicas al Cisco 831
(en la foto aún sin conectar) y detrás de este (en el diagrama), un ASA 5505 (arriba de todo en la foto).

Verificación
Router#sh crypto isakmp
sa (verificación fase I IPsec)
IPv4 Crypto ISAKMP SA
dst src state
conn-id slot status
200.80.209.92 200.80.209.89 QM_IDLE
1079 0 ACTIVE
IPv6 Crypto ISAKMP SA
Router#sh crypto ipsec
sa (verificación fase II IPsec)
interface: FastEthernet0/1
Crypto map tag: VPN, local addr 200.80.209.92
protected vrf: (none)
local ident
(addr/mask/prot/port): (10.0.0.0/255.0.0.0/0/0)
remote ident (addr/mask/prot/port):
(192.168.1.0/255.255.255.0/0/0)
current_peer 200.80.209.89 port 4500 (en
vez de UDP 500 porque está detrás de un NAT)
PERMIT, flags={}
#pkts encaps: 69961, #pkts encrypt: 69961, #pkts
digest: 69961
#pkts decaps: 139566, #pkts decrypt: 139566,
#pkts verify: 139566
#pkts compressed: 0, #pkts decompressed: 0
#pkts not compressed: 0, #pkts compr. failed: 0
#pkts not decompressed: 0, #pkts decompress failed: 0
#send errors 0, #recv errors 0
---resumido---
Router#sh ip route (verificación enrutamiento)
Gateway of last resort is
200.80.209.89 to network 0.0.0.0
200.80.209.0/29 is subnetted, 1 subnets
C 200.80.209.88 is directly connected,
FastEthernet0/1
10.0.0.0/16 is subnetted, 1 subnets
C 10.61.0.0 is directly connected,
FastEthernet0/0
S 192.168.1.0/24 [1/0] via 200.80.209.89 (router
ADSL, ruta creada cuando levanta la VPN)
S* 0.0.0.0/0 [1/0] via 200.80.209.89 (default gateway)
Router#
Gateway# sh ip nat
trans (verificamos PAT hacia internet)
Pro Inside global Inside local Outside local
Outside global
udp
200.80.209.89:4500 192.168.0.2:4500 200.80.209.92:4500 200.80.209.92:4500 (non-isakmp, detrás de NAT)
Gateway#
FW-ASA# sh crypto
isakmp sa (verificación fase I)
Active SA: 1
Rekey SA: 0 (A tunnel will report 1 Active and 1 Rekey SA
during rekey)
Total IKE SA: 1
1 IKE Peer: 200.80.209.92
Type : L2L Role : initiator (ASA inició el
túnel)
Rekey : no State : MM_ACTIVE
FW-ASA# sh crypto ipsec
sa (verificación fase II)
interface: outside
Crypto map tag: Outside, seq num: 1, local addr: 192.168.0.2
access-list outside_1_cryptomap permit ip 192.168.1.0
255.255.255.0 10.0.0.0 255.0.0.0
local ident (addr/mask/prot/port):
(192.168.1.0/255.255.255.0/0/0)
remote ident (addr/mask/prot/port): (10.0.0.0/255.0.0.0/0/0)
current_peer: 200.80.209.92
#pkts encaps: 139566, #pkts encrypt: 139566,
#pkts digest: 139566
#pkts decaps: 69961, #pkts decrypt: 69961,
#pkts verify: 69961
#pkts compressed: 0, #pkts decompressed: 0
#pkts not compressed: 139566, #pkts comp failed: 0, #pkts
decomp failed: 0
#pre-frag successes: 0, #pre-frag failures: 0, #fragments
created: 0
#PMTUs sent: 0, #PMTUs rcvd: 0, #decapsulated frgs needing
reassembly: 0
#send errors: 0, #recv errors: 0
local crypto endpt.: 192.168.0.2/4500,
remote crypto endpt.: 200.80.209.92/4500 (porque
está detrás de un NAT)
path mtu 1500, ipsec overhead 66, media mtu 1500
current outbound spi: CB46D829
FW-ASA# sh route (verificación enrutamiento)
Gateway of last resort is
192.168.0.1 to network 0.0.0.0
C 127.1.0.0 255.255.0.0 is directly
connected, _internal_loopback
C 192.168.0.0 255.255.255.0 is directly
connected, outside
C 192.168.1.0 255.255.255.0 is directly
connected, inside
S* 0.0.0.0 0.0.0.0 [1/0] via 192.168.0.1,
outside (router ADSL con PAT)
FW-ASA#
Cambios en la IP del router
Cisco 831 simulando IP dinámica
Gateway#
Gateway#conf t
Enter configuration
commands, one per line. End with
CNTL/Z.
Gateway(config)#int
eth1
Gateway(config-if)#ip
add 200.80.209.90 255.255.255.248 (nueva IP del router
ADSL)
Gateway(config-if)#^Z
Gateway#
Router#sh crypto isakm
sa (verificación fase I)
IPv4 Crypto ISAKMP SA
dst src state
conn-id slot status
200.80.209.92 200.80.209.89 QM_IDLE
1079 0 ACTIVE (luego quedará como DELETED)
200.80.209.92 200.80.209.90 QM_IDLE
1080 0 ACTIVE (nueva IP del router ADSL)
Router#sh ip route (verificación enrutamiento)
Gateway of last resort is
200.80.209.89 to network 0.0.0.0
200.80.209.0/29 is subnetted, 1 subnets
C 200.80.209.88 is directly connected,
FastEthernet0/1
10.0.0.0/16 is subnetted, 1 subnets
C 10.61.0.0 is directly connected,
FastEthernet0/0
S 192.168.1.0/24 [1/0] via 200.80.209.90 (nueva IP del router ADSL generada por IPSec)
S* 0.0.0.0/0 [1/0] via 200.80.209.89 (default gateway, no impacta)
Router#
Configuraciones relevantes en
los equipos
Router#sh runn (terminador de tunel)
Building configuration...
Current configuration :
2111 bytes
!
version 12.4
!
hostname Router
!
crypto isakmp policy 1
hash md5
authentication pre-share
group 5
!
crypto isakmp key cisco123
address 0.0.0.0 (acepta cualquier IP)
crypto isakmp nat
keepalive 10
!
!
crypto ipsec transform-set
DES-MD5 esp-des esp-md5-hmac
crypto ipsec
nat-transparency spi-matching
!
crypto dynamic-map vpn-adsl
10 (es dinámico ya que se adapta a cualquier IP)
set transform-set DES-MD5
set pfs group5
match address VPN (ver ACL VPN)
reverse-route (genera una entrada en
la tabla de enrutamiento)
!
crypto map VPN 1
ipsec-isakmp dynamic vpn-adsl (asocia dinámico
con mapa en la interfaz)
!
interface FastEthernet0/0
ip address 10.61.1.1 255.255.0.0
ip nat inside
ip virtual-reassembly
!
interface FastEthernet0/1
ip address 200.80.209.92 255.255.255.248
ip nat outside
ip virtual-reassembly
crypto map VPN (mapa de cifrado real)
!
ip nat inside source
route-map SDM_RMAP_1 interface FastEthernet0/1 overload
! (también podría utilizarse ip nat inside source list NAT etc...)
!
ip access-list extended
NAT
deny ip 10.0.0.0
0.255.255.255 192.168.1.0 0.0.0.255 (evita NAT,
reencapsula tráfico)
permit ip 10.0.0.0 0.255.255.255 any
ip access-list extended
VPN
permit ip 10.0.0.0 0.255.255.255 192.168.1.0 0.0.0.255 (tráfico a enviar a la VPN)
!
route-map SDM_RMAP_1
permit 1
match ip address NAT
!
end
Gateway#sh runn (delante del ASA)
Building configuration...
Current configuration :
1694 bytes
!
version 12.2
!
hostname Gateway
!
interface Ethernet0
description INSIDE
ip address 192.168.0.1 255.255.255.0
ip nat inside
!
interface Ethernet1
description OUTSIDE
ip address 200.80.209.89 255.255.255.248
ip nat outside
!
(ver que no existe
port forwarding, lo que fuerza al ASA a ser iniciador del túnel)
!
ip nat inside source list
NAT interface Ethernet1 overload (PAT)
!
ip access-list extended
NAT
permit ip 192.168.0.0 0.0.0.255 any
!
end
FW-ASA# sh runn (terminador de tunel)
ASA Version 7.2(3)
!
hostname FW-ASA
!
interface Vlan1
nameif inside
security-level 100
ip address 192.168.1.1 255.255.255.0
!
interface Vlan2
nameif outside
security-level 0
ip address 192.168.0.2 255.255.255.0
!
interface Ethernet0/0
switchport access vlan 2
!
interface Ethernet0/1
!
access-list
outside_1_cryptomap extended permit ip 192.168.1.0 255.255.255.0 10.0.0.0
255.0.0.0 (tráfico a la VPN)
!
access-list
inside_nat0_outbound extended permit ip 192.168.1.0 255.255.255.0 10.0.0.0 255.0.0.0
!
global (outside) 1
interface
nat (inside) 0 access-list
inside_nat0_outbound (evita NAT, reencapsula
tráfico)
nat (inside) 1 192.168.1.0
255.255.255.0
!
route outside 0.0.0.0
0.0.0.0 192.168.0.1 1 (vía el router ADSL)
!
crypto ipsec transform-set
ESP-DES-MD5 esp-des esp-md5-hmac (fase II IPSec)
crypto map Outside 1 match
address outside_1_cryptomap (fase II IPSec)
crypto map Outside 1 set
pfs group5 (fase II IPSec)
crypto map Outside 1 set
peer 200.80.209.92 (fase II IPSec)
crypto map Outside 1 set
transform-set ESP-DES-MD5 (fase II IPSec)
crypto map Outside
interface outside (fase II IPSec)
crypto isakmp enable
outside (fase I IPSec)
crypto isakmp policy 10 (fase I IPSec)
authentication pre-share
encryption des
hash md5
group 5
lifetime 86400
crypto isakmp
nat-traversal 10 (fase I IPSec)
!
policy-map global_policy
class inspection_default
inspect dns preset_dns_map
inspect ftp
---resumido---
inspect sip
inspect xdmcp
inspect icmp (permite los Ping)
inspect icmp error (permite Tracert)
!
service-policy
global_policy global (todas las interfaces)
!
tunnel-group 200.80.209.92
type ipsec-l2l
tunnel-group 200.80.209.92
ipsec-attributes (fase I IPSec)
pre-shared-key * (cisco123)
: end
Pruebas de performance entre
extremos
Utilizando el túnel, notar que están conectados a 10 Mbps mediante en router Gateway, en la configuración aparece
como Eth0 y 1, por lo tanto el
límite de ambas inetrfaces es 10 Mbps menos las cabeceras IPSec.
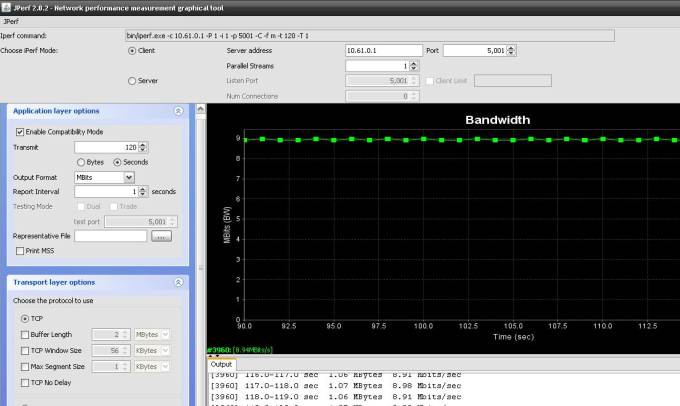
bin/iperf.exe -c 10.61.0.1 -P 1 -i 1
-p 5001 -C -f m -t 120 -T 1
------------------------------------------------------------
Client connecting to 10.61.0.1, TCP
port 5001
TCP window size: 0.01 MByte (default)
------------------------------------------------------------
[3960] local 192.168.1.123 port
1458 connected with 10.61.0.1 port 5001
[ ID] Interval Transfer Bandwidth
[3960] 0.0- 1.0 sec 1.07
MBytes 8.98 Mbits/sec
[3960] 1.0- 2.0 sec 1.06
MBytes 8.91 Mbits/sec
[3960] 2.0- 3.0 sec 1.07
MBytes 8.98 Mbits/sec
---resumido---
[3960] 113.0-114.0 sec 1.06 MBytes
8.91 Mbits/sec
[3960] 114.0-115.0 sec 1.06 MBytes
8.91 Mbits/sec
[3960] 115.0-116.0 sec 1.07 MBytes
8.98 Mbits/sec
[3960] 116.0-117.0 sec 1.06 MBytes
8.91 Mbits/sec
[3960] 117.0-118.0 sec 1.07 MBytes
8.98 Mbits/sec
[3960] 118.0-119.0 sec 1.06 MBytes
8.91 Mbits/sec
[3960] 119.0-120.0 sec 1.07 MBytes
8.98 Mbits/sec
[ ID] Interval Transfer Bandwidth
[3960] 0.0-120.0 sec 128 MBytes 8.94 Mbits/sec (promedio)
Done.
(2012) Datacenters stories by uncle Ernst
Rosario, Argentina