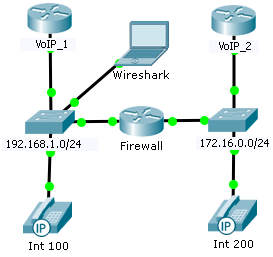
Escenario de VoIP a través de un firewall ZBF
Fecha: 29 de abril del 2015 Clase: CCNA Security
Escenario
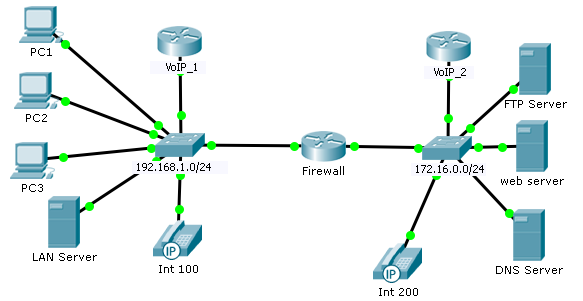
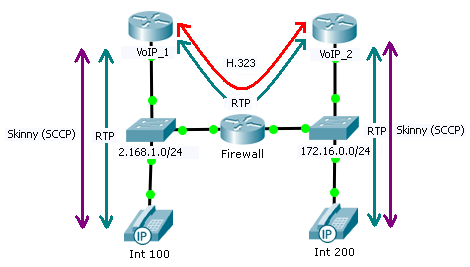
Este
escenario es una implementación de firewall basado en zonas (ZBF)
correspondiente al módulo 5 de CCNASEc
versión
1.1, donde se configuraron dos zonas: segura (192.168.1.0/24) que nuestra LAN e
insegura (172.16.0.0/24) que
es
una LAN no administrada por nosotros, pero que debemos acceder a servisores y
que luego se agregó la situación
de
implemntar VoIP, donde debemos permitir la señalización H.323 entre ambas
centrales VoIP, implementadas
mediante
routers con call manager express (CME).
Este
escenario se realizó en Packet Tracer y se verificó con equipos reales: Cisco
2801 para el ZBF y 1760 para CME.
El archivo
está disponible como Prueba ZBF con
VoIP.pkt en ftp.vilarrasa.com.ar
user y pass: ccna.
1.- Verificación inicial del funcionamiento de la telefonía IP
Se verifica
en el entorno local, entre el teléfono y el router con call manager sin pasar
por el firewall.
El protocolo
que utilizan los teléfonos localmente es SCCP (Skinny).
VoIP_1#sh ephone
ephone-1
Mac:0040.0B47.E119 TCP socket:[1] activeLine:0 REGISTERED in SCCP ver 12 and Server in ver 8
mediaActive:0
offhook:0 ringing:0 reset:0 reset_sent:0 paging 0 debug:0 caps:8
IP:192.168.1.3 1025 7960 keepalive 43
max_line 2
button
1: dn 1 number 100 CH1 IDLE
VoIP_1#
VoIP_2#sh ephone
ephone-1
Mac:0001.C966.A163 TCP socket:[1] activeLine:0 REGISTERED in SCCP ver 12 and Server in ver 8
mediaActive:0
offhook:0 ringing:0 reset:0 reset_sent:0 paging 0 debug:0 caps:8
IP:172.16.0.3 1025 7960 keepalive 43
max_line 2
button
1: dn 1 number 200 CH1 IDLE
VoIP_2#
2.- Agregado del class-map que clasifica el tráfico de
señalización entre los CME:
Firewall#config t
Firewall(config)#class-map type inspect match-any
VoIP_Signal
Firewall(config-cmap)#match protocol h323
Firewall(config-cmap)#exit
Firewall(config)#
3.- Agregado del class-map que clasifica el tráfico de voice
(audio) entre los CME:
Firewall#config t
Firewall(config-cmap)#class-map type inspect match-any VoIP_Voice
Firewall(config-cmap)#match protocol udp
Firewall(config-cmap)#exit
Firewall(config)#
4.- Asociamos los class-map a la política de tráfico saliente
hacia la red 172.16.0.0/24:
Firewall(config)#policy-map type inspect policy1
Firewall(config-pmap)#class type inspect VoIP_Signal
Firewall(config-pmap-c)#inspect
Firewall(config-pmap-c)#class type inspect VoIP_Voice
Firewall(config-pmap-c)#inspect
Firewall(config-pmap-c)#exit
Firewall(config-pmap)#exit
Firewall(config)#
5.- Asociamos los class-map a la política de tráfico entrante
desde la red 172.16.0.0/24:
Firewall(config)#policy-map type inspect policy2
Firewall(config-pmap)#class type inspect VoIP_Signal
Firewall(config-pmap-c)#inspect
Firewall(config-pmap-c)#class type inspect VoIP_Voice
Firewall(config-pmap-c)#inspect
Firewall(config-pmap-c)#exit
Firewall(config-pmap)#exit
Firewall(config)#
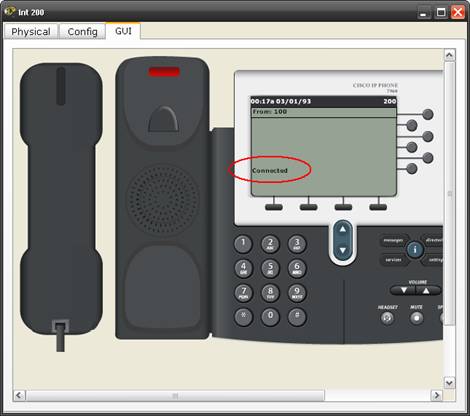
6.- Realización de una llamada entre el interno 100 (izquierda,
zona segura) al 200 (derecha, zona insegura):
Esta
comunicación utiliza el zone-pair segura-insegura asociado a la policy1, esto
genera tráfico H.323.
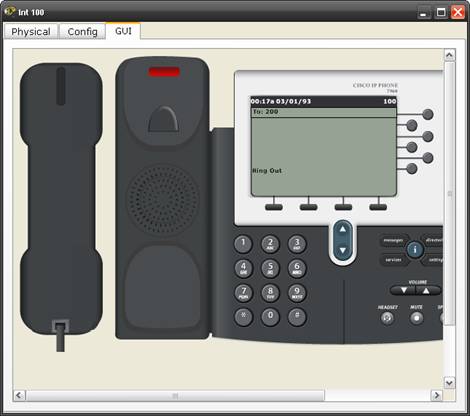
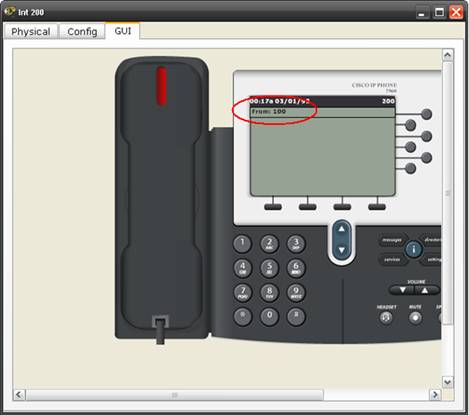
Al descolgar
y atender la llamada se comienza a utilizar el canal RTP, con la voz
propiamente dicha.
7.- Verificación en el firewall:
Firewall#show policy-map
type inspect zone-pair sessions
Zone-pair: segura-insegura
Service-policy inspect : policy1 (para llamadas desde el interno 100 al 200)
Class-map: saliente (match-any)
Match: protocol dns
0 packets, 0 bytes
30 second rate 0 bps
Match: protocol ftp
0 packets, 0 bytes
30 second rate 0 bps
Match: protocol http
0 packets, 0 bytes
30 second rate 0 bps
Inspect
Class-map: ICMP (match-any)
Match: protocol icmp
0 packets, 0 bytes
30 second rate 0 bps
Inspect
Class-map:
VoIP_Signal (match-any)
Match:
protocol h323 (este es el
canal de señalización (conversación) entre gateways VoIP)
8
packets, 327 bytes
30
second rate 0 bps
Inspect
Established Sessions
Session 139927312 (192.168.1.2:1025)=>(172.16.0.2:1720)
tcp SIS_OPEN/TCP_ESTAB
Created 00:03:09, Last heard 00:02:32
Bytes sent (initiator:responder) [534:0]
Class-map:
VoIP_Voice (match-any)
Match:
protocol udp (este es el canal
RTP para la voz propiamente dicha)
11
packets, 330 bytes
30
second rate 0 bps
Pass
Established Sessions
Session 140124328 (192.168.1.2:1026)=>(172.16.0.2:1026)
udp SIS_OPEN
Created 00:02:32, Last heard 00:00:02
Bytes sent (initiator:responder) [660:0]
Class-map: class-default (match-any)
Match: any
Drop (default action)
0 packets, 0 bytes
Zone-pair: insegura-segura
Service-policy inspect : policy2 (para llamadas entrantes)
Class-map: entrante (match-any) (para acceder al LAN server)
Match: protocol http
0 packets, 0 bytes
30 second rate 0 bps
Inspect
Class-map:
VoIP_Signal (match-any) (no hay sesiones
porque en esta comunicación el trafico al
Match:
protocol h323
originarse en el
interno 100 es sólo de retorno)
8
packets, 327 bytes
30
second rate 0 bps
Inspect
Class-map:
VoIP_Voice (match-any)
Match:
protocol udp
11
packets, 330 bytes
30
second rate 0 bps
Pass
Class-map: ICMP (match-any)
Match: protocol icmp
0 packets, 0 bytes
30 second rate 0 bps
Drop
0 packets, 0 bytes
Class-map: class-default (match-any)
Match: any
Drop (default action)
0 packets, 0 bytes
Firewall#
8.- Realización de una llamada entre el interno 200 (derecha, zona
insegura) al 100 (izquierda, zona segura):
Esta
comunicación utiliza el zone-pair insegura-segura asociado a la policy2.

9.- Verificación de la policy2:
Firewall#show policy-map
type inspect zone-pair sessions
Zone-pair: segura-insegura
Service-policy inspect : policy1
Class-map: saliente (match-any)
Match: protocol dns
0 packets, 0 bytes
30 second rate 0 bps
Match: protocol ftp
0 packets, 0 bytes
30 second rate 0 bps
Match: protocol http
0 packets, 0 bytes
30 second rate 0 bps
Inspect
Class-map: ICMP (match-any)
Match: protocol icmp
0 packets, 0 bytes
30 second rate 0 bps
Inspect
Class-map: VoIP_Signal (match-any)
Match: protocol h323
14 packets, 573 bytes
30 second rate 0 bps
Inspect
Established Sessions
Session 139927312 (192.168.1.2:1025)=>(172.16.0.2:1720)
tcp SIS_OPEN/TCP_ESTAB
Created 00:04:36, Last heard 00:01:02
Bytes sent (initiator:responder) [615:0]
Class-map: VoIP_Voice (match-any)
Match: protocol udp
14 packets, 420 bytes
30 second rate 0 bps
Pass
Class-map: class-default (match-any)
Match: any
Drop (default action)
0 packets, 0 bytes
Zone-pair: insegura-segura
Service-policy inspect : policy2
Class-map: entrante (match-any)
Match: protocol http
0 packets, 0 bytes
30 second rate 0 bps
Inspect
Class-map:
VoIP_Signal (match-any)
Match:
protocol h323 (este es el
canal de señalización (conversación) entre gateways VoIP)
14 packets, 573 bytes
30 second rate 0 bps
Inspect
Established Sessions
Session 141127656 (172.16.0.2:1025)=>(192.168.1.2:1720)
tcp SIS_OPEN/TCP_ESTAB
Created 00:00:57, Last heard 00:00:26
Bytes sent (initiator:responder)
[205:126]
Class-map:
VoIP_Voice (match-any)
Match:
protocol udp (este es el canal
RTP para la voz propiamente dicha)
14 packets, 420 bytes
30 second rate 0 bps
Pass
Established Sessions
Session 140124328 (172.16.0.2:1027)=>(192.168.1.2:1027)
udp SIS_OPEN
Created 00:00:26, Last heard 00:00:11
Bytes sent (initiator:responder) [60:60]
Class-map: ICMP (match-any)
Match: protocol icmp
0 packets, 0 bytes
30 second rate 0 bps
Drop
0 packets, 0 bytes
Class-map: class-default (match-any)
Match: any
Drop (default action)
0 packets, 0 bytes
Firewall#
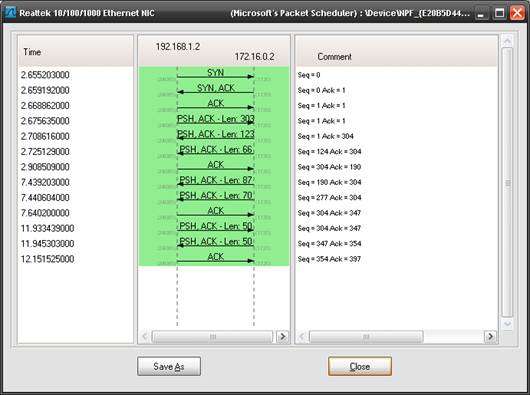
10.- Pruebas de verificación
con equipos reales:
Para ganar
tiempo con las pruebas, en reemplazo de los teléfonos IP, se utilizaron
softphones Cisco IP communicator
en
dos notebooks y se realizó la captura de tráfico mediante Wireshark y un port
mirror en el switch.

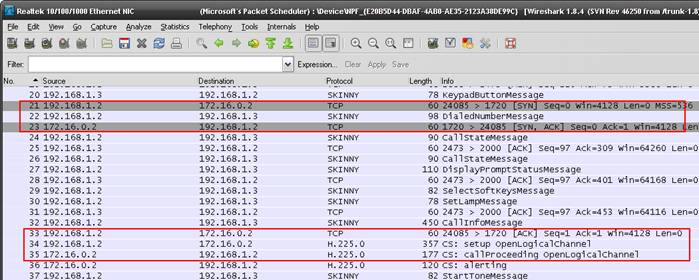
Puede observarse
el diálogo H.323 entre los gateways VoIP, el puerto TCP 1720 corresponde a
H.323 y H.225 es parte de la suite H.323.

11.- Verificación del ZBF:
Firewall#sh policy-map type inspect zone-pair
sessions
Zone-pair: segura-insegura
Service-policy inspect :
policy1
Class-map: VoIP_Voice
(match-any)
Match: protocol udp
0 packets, 0 bytes (no se utilizó este class-map)
30 second rate 0 bps
Inspect
Class-map: ICMP (match-any)
Match: protocol icmp
3 packets, 108 bytes
30 second rate 0 bps
Inspect
Class-map: VoIP_Signal
(match-any)
Match: protocol h323
7 packets, 168 bytes
30 second rate 0 bps
Inspect
Established Sessions
Session 64332304 (192.168.1.2:16824)=>(172.16.0.2:17984) h323-RTP-audio SIS_OPEN
Created 00:00:05, Last heard 00:00:00
Bytes sent (initiator:responder) [9536:9216]
Session 64331824 (192.168.1.2:16825)=>(172.16.0.2:17985) h323-RTCP-audio SIS_OPEN
Created 00:00:03, Last heard 00:00:00
Bytes sent (initiator:responder) [264:224]
Session 643325BC (192.168.1.2:24669)=>(172.16.0.2:1720) h323
SIS_OPEN
Created 00:01:48, Last heard 00:00:05
Bytes sent (initiator:responder) [656:742]
Pre-generated
Sessions (se generaron
sesiones UDP derivadas del propio H.323)
Pre-gen session 6433156C 192.168.1.2[1024:65535]=>172.16.0.2[17985:17985]
h323-RTCP-audio
Pre-gen session 64331ADC 172.16.0.2[1024:65535]=>192.168.1.2[16825:16825]
h323-RTCP-audio
Pre-gen session 64331D94 172.16.0.2[1024:65535]=>192.168.1.2[16824:16824]
h323-RTP-audio
Pre-gen session 6433204C 172.16.0.2[1024:65535]=>192.168.1.2[16825:16825]
h323-RTCP-audio
Class-map: saliente
(match-any)
Match: protocol ftp
0 packets, 0 bytes
30 second rate 0 bps
Match: protocol http
0 packets, 0 bytes
30 second rate 0 bps
Match: protocol dns
0 packets, 0 bytes
30 second rate 0 bps
Pass
0 packets, 0 bytes
Class-map:
class-default (match-any)
Match: any
Drop (default action)
0 packets, 0 bytes
Zone-pair: insegura-segura
Service-policy inspect :
policy2
Class-map: entrante (match-any)
Match: protocol http
0 packets, 0 bytes
30 second rate 0 bps
Inspect
Class-map: VoIP_Signal (match-any)
Match: protocol h323
0 packets, 0 bytes
30 second rate 0 bps
Inspect
Class-map: VoIP_Voice (match-any)
Match: protocol udp
0 packets, 0 bytes
30 second rate 0 bps
Pass
0 packets, 0 bytes
Class-map: ICMP (match-any)
Match: protocol icmp
0 packets, 0 bytes
30 second rate 0 bps
Drop
0 packets, 0 bytes
Class-map: class-default (match-any)
Match: any
Drop (default action)
0 packets, 0 bytes
Firewall#
12.- Contraprueba, se desafectó de las policy1 y 2 el class-map de
voice (audio):
Firewall(config)#policy-map type inspect policy1
Firewall(config-pmap)#no class type inspect VoIP_Voice
Firewall(config-pmap)#exit
Firewall(config)#policy-map type inspect policy2
Firewall(config-pmap)#no class type inspect VoIP_Voice
Firewall(config-pmap)#^Z
Firewall#
13.- Verificación:
Se estableció
la comunicación sin problemas de audio entre ambos softphones.
Firewall#sh policy-map type inspect zone-pair
sessions
Zone-pair: segura-insegura
Service-policy inspect :
policy1 (no existe el class-map VoIP_Voice)
Class-map: ICMP (match-any)
Match: protocol icmp
3 packets, 108 bytes
30 second rate 0 bps
Inspect
Class-map: VoIP_Signal
(match-any)
Match: protocol h323
7 packets, 168 bytes
30 second rate 0 bps
Inspect
Established
Sessions
Session 6433156C (172.16.0.2:17131)=>(192.168.1.2:17359) h323-RTCP-audio SIS_OPEN
Created 00:00:10, Last heard 00:00:00
Bytes sent (initiator:responder) [336:528]
Session 64331824 (192.168.1.2:17358)=>(172.16.0.2:17130) h323-RTP-audio SIS_OPEN
Created 00:00:10, Last heard 00:00:00
Bytes sent (initiator:responder) [16704:16352]
Session 643325BC (192.168.1.2:24669)=>(172.16.0.2:1720) h323 SIS_OPEN
Created 00:11:08, Last heard 00:00:10
Bytes sent (initiator:responder) [1009:1138]
Pre-generated
Sessions
Pre-gen session 64332304 192.168.1.2[1024:65535]=>172.16.0.2[17131:17131]
h323-RTCP-audio
Pre-gen session 6433204C 172.16.0.2[1024:65535]=>192.168.1.2[17359:17359]
h323-RTCP-audio
Pre-gen session 64331D94 172.16.0.2[1024:65535]=>192.168.1.2[17358:17358]
h323-RTP-audio
Pre-gen session 64331ADC 192.168.1.2[1024:65535]=>172.16.0.2[17131:17131]
h323-RTCP-audio
Class-map: saliente (match-any)
Match: protocol ftp
0 packets, 0 bytes
30 second rate 0 bps
Match: protocol http
0 packets, 0 bytes
30 second rate 0 bps
Match: protocol dns
0 packets, 0 bytes
30 second rate 0 bps
Pass
0 packets, 0 bytes
Class-map: class-default (match-any)
Match: any
Drop (default action)
0 packets, 0 bytes
Zone-pair: insegura-segura
Service-policy inspect : policy2
Class-map: entrante (match-any)
Match: protocol http
0 packets, 0 bytes
30 second rate 0 bps
Inspect
Class-map: VoIP_Signal (match-any)
Match: protocol h323
0 packets, 0 bytes
30 second rate 0 bps
Inspect
Class-map: ICMP (match-any)
Match: protocol icmp
1 packets, 36 bytes
30 second rate 0 bps
Drop
1
packets, 36 bytes
Class-map: class-default (match-any)
Match: any
Drop (default action)
0 packets, 0 bytes
Firewall#
14.- Llamada en sentido inverso (interno 200 a 100):
Firewall#sh policy-map type inspect zone-pair
sessions
Zone-pair: segura-insegura
Service-policy inspect : policy1
Class-map: ICMP (match-any)
Match: protocol icmp
4 packets, 144 bytes
30 second rate 0 bps
Inspect
Class-map: VoIP_Signal (match-any)
Match: protocol h323
7 packets, 168 bytes
30 second rate 0 bps
Inspect
Established Sessions
Session 643325BC (192.168.1.2:24669)=>(172.16.0.2:1720) h323 SIS_OPEN
Created 00:14:33, Last heard 00:00:15
Bytes sent (initiator:responder) [1059:1188]
Class-map: saliente (match-any)
Match: protocol ftp
0 packets, 0 bytes
30 second rate 0 bps
Match: protocol http
0 packets, 0 bytes
30 second rate 0 bps
Match: protocol dns
0 packets, 0 bytes
30 second rate 0 bps
Pass
0 packets, 0 bytes
Class-map: class-default (match-any)
Match: any
Drop (default action)
0 packets, 0 bytes
Zone-pair: insegura-segura
Service-policy inspect : policy2
Class-map: entrante (match-any)
Match: protocol http
0 packets, 0 bytes
30 second rate 0 bps
Inspect
Class-map: VoIP_Signal
(match-any)
Match: protocol h323
3 packets, 72 bytes
30 second rate 0 bps
Inspect
Established Sessions
Session 64331ADC (172.16.0.2:61553)=>(192.168.1.2:1720) h323 SIS_OPEN
Created 00:00:11, Last heard 00:00:08
Bytes sent (initiator:responder) [303:420]
Session 64331D94 (172.16.0.2:18416)=>(192.168.1.2:17086) h323-RTP-audio SIS_OPEN
Created 00:00:08, Last heard 00:00:00
Bytes sent (initiator:responder) [13312:13312]
Session 64330FFC (172.16.0.2:18417)=>(192.168.1.2:17087) h323-RTCP-audio SIS_OPEN
Created 00:00:07, Last heard 00:00:03
Bytes sent (initiator:responder) [224:264]
Pre-generated
Sessions
Pre-gen session 6433204C 172.16.0.2[1024:65535]=>192.168.1.2[17087:17087]
h323-RTCP-audio
Pre-gen session 64332304 192.168.1.2[1024:65535]=>172.16.0.2[18417:18417]
h323-RTCP-audio
Pre-gen session 643312B4 192.168.1.2[1024:65535]=>172.16.0.2[18416:18416]
h323-RTP-audio
Pre-gen session 64330D44 192.168.1.2[1024:65535]=>172.16.0.2[18417:18417]
h323-RTCP-audio
Class-map: ICMP (match-any)
Match: protocol icmp
1 packets, 36 bytes
30 second rate 0 bps
Drop
1 packets, 36 bytes
Class-map: class-default (match-any)
Match: any
Drop (default action)
0 packets, 0 bytes
Firewall#
Por los
resultados de las capturas y el monitoreo del firewall se determina que el
flujo de tráfico es el siguiente:
15.- Configuración de equipos (en Packet Tracer):
Firewall#sh runn (sólo lo mas relevante)
!
version
12.4
!
hostname
Firewall
!
class-map
type inspect match-any saliente
match
protocol dns
match
protocol ftp
match
protocol http
class-map
type inspect match-any ICMP
match
protocol icmp
class-map
type inspect match-any entrante
match
protocol http
class-map
type inspect match-any VoIP_Signal
match
protocol h323
class-map
type inspect match-any VoIP_Voice
match
protocol udp
!
policy-map
type inspect policy2
class
type inspect entrante
inspect
class
type inspect VoIP_Signal
inspect
class
type inspect VoIP_Voice
pass
class
type inspect ICMP
drop
!
policy-map
type inspect policy1
class
type inspect saliente
inspect
class
type inspect ICMP
inspect
class
type inspect VoIP_Signal
inspect
class
type inspect VoIP_Voice
pass
!
zone
security segura
zone
security insegura
zone-pair
security segura-insegura source segura destination insegura
service-policy
type inspect policy1
zone-pair
security insegura-segura source insegura destination segura
service-policy
type inspect policy2
!
!
interface
FastEthernet0/0
ip
address 192.168.1.1 255.255.255.0
zone-member
security segura
!
interface
FastEthernet0/1
ip
address 172.16.0.1 255.255.255.0
zone-member
security insegura
!
end
Firewall#
VoIP_1# sh runn (sólo lo mas relevante)
!
version
12.4
!
hostname
VoIP_1
!
ip
dhcp pool VoIP
network
192.168.1.0 255.255.255.0
default-router
192.168.1.1
option
150 ip 192.168.1.2
!
interface
FastEthernet0/0
ip
address 192.168.1.2 255.255.255.0
!
ip
route 0.0.0.0 0.0.0.0 192.168.1.1
!
dial-peer
voice 1 voip
destination-pattern
20.
session
target ipv4:172.16.0.2
!
telephony-service
max-ephones
10
max-dn
10
ip
source-address 192.168.1.2 port 2000
auto
assign 1 to 4
!
ephone-dn
1
number
100
!
ephone
1
device-security-mode
none
mac-address
0040.0B47.E119
type
7960
button
1:1
!
end
VoIP_1#
VoIP_2# sh runn (sólo lo mas relevante)
!
version
12.4
!
hostname
VoIP_2
!
ip
dhcp pool VoIP
network
172.16.0.0 255.255.255.0
default-router
172.16.0.1
option
150 ip 172.16.0.2
!
interface
FastEthernet0/0
ip
address 172.16.0.2 255.255.255.0
!
ip
route 0.0.0.0 0.0.0.0 172.16.0.1
!
dial-peer
voice 1 voip
destination-pattern
10.
session
target ipv4:192.168.1.2
!
telephony-service
max-ephones
10
max-dn
10
ip
source-address 172.16.0.2 port 2000
auto
assign 1 to 4
!
ephone-dn
1
number
200
!
ephone
1
device-security-mode
none
mac-address
0001.C966.A163
type
7960
button
1:1
!
end
VoIP_2#
(2015)
Smoking chala with uncle Ernst
Rosario,
Argentina